Looks like AMD Ryzen has the same problem as Intel with Security Vulnerabilities
13 critical security vulnerabilities and manufacturer backdoors discovered in amd ryzen processors
-
2018-03-13, 06:45 PM #1
13 Security Vulnerabilities and Manufacturer Backdoors Exposed In AMD Ryzen Processor
AMD Ryzen 7 7800X3D: Gigabyte X670 Aorus Elite AX: G.Skill Trident Z5 Neo RGB DDR5-6000 C30 : PowerColor Radeon RX 7900 GRE Hellhound OC: CORSAIR HX850i: Samsung 960 EVO 250GB NVMe: fiio e10k: lian-li pc-o11 dynamic XL:
-
2018-03-13, 06:54 PM #2
Quote from the news:
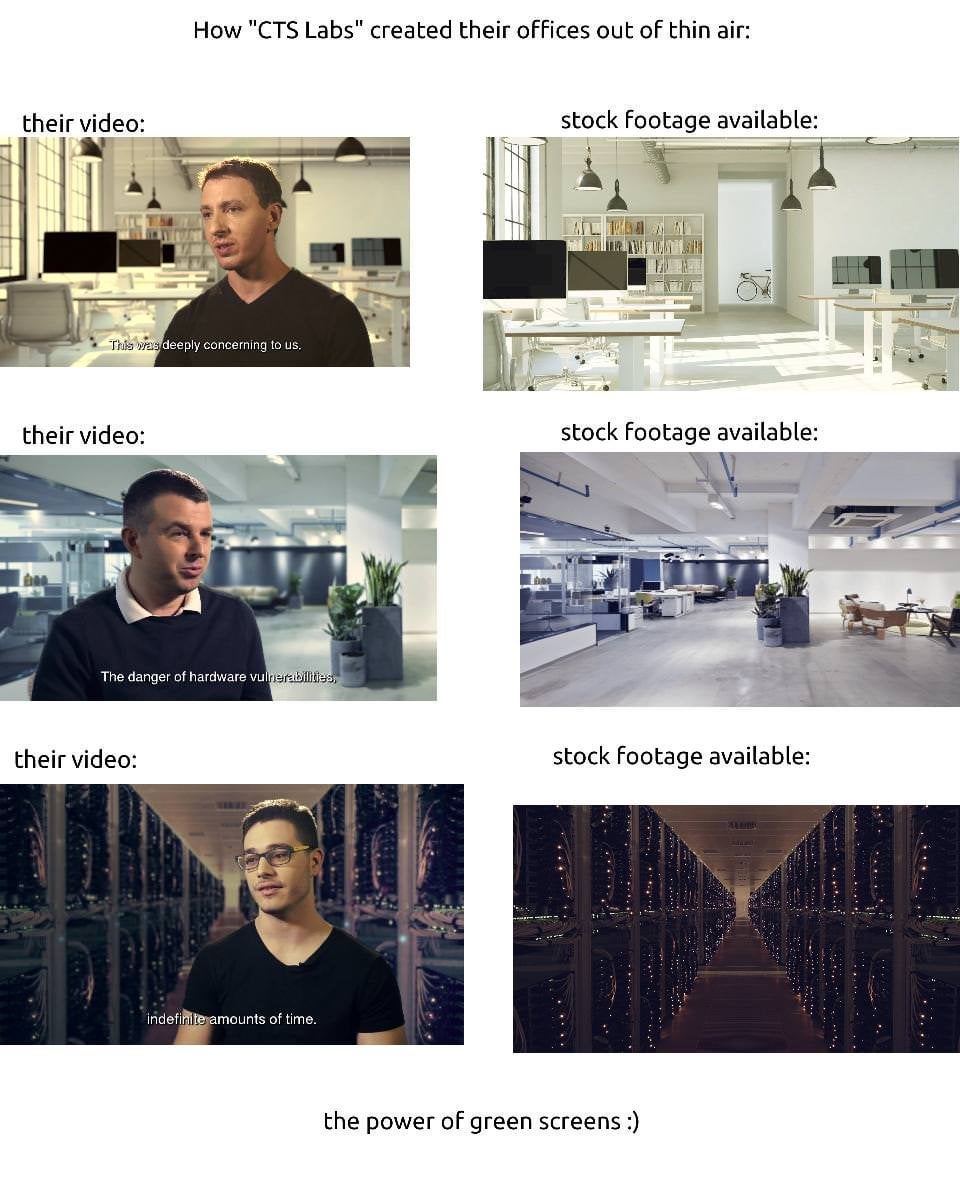
We will see if this is legit or not.CTS Labs has produced a white paper report further detailing these vulnerabilities available at amdflaws.com. Honestly, with all the naming like amdflaws, Ryzenfall etc you'd figure a certain 'other' company would be behind CST Labs, or this to be some #fakenews. While possible, that does seem too far-fetched though, but the way information was managed and released is rather 'smelly'. The entire disclosure of all this content seems and feels like a marketing campaign, with a video on a fresh youtube video of a guy in front of a green screen, with the YT channel made just for this announcement, the amdflaws website created merely late February. It all feels ...very weird.
-
2018-03-13, 06:55 PM #3
Yep, this is theoretically possible.
However this would require physical access to the machine at all times as all of the mentioned issues are in the white paper as an "opinion" believe it or not.
Followed by the fact that you need to flash a BIOS onto the machine that contains both the functional BIOS and the malware.
Followed by that they also have to then install the malware software to utilize these issues in Windows/Linux/UNIX based OS, etc.
With all of the above no single system is really safe, not Intel, not AMD, not IBM and not VIA (there's plenty more other brands).
Not sure whether this should be taken seriously as this would mean you pretty much own the hardware already and nothing can be launched from a distance.
Also do you know of server hardware that allows for BIOS updating that isn't encrypted and/or sum checked for validity?
ASUS boards are the only ones I know of that allow you to bypass this and it's only present on their consumer boards with USB Bios FlashBack.
This is a little bit of a "wut?" for crypto-security for me, unsure whether to take it serious or not.
Also these guys completely ignored the 90-day industry wide accepted standard for these things and gave AMD only 24 hours to respond.
Sounds a little vindictive don't you think?"A quantum supercomputer calculating for a thousand years could not even approach the number of fucks I do not give."
- Kirito, Sword Art Online Abridged by Something Witty Entertainment
-
2018-03-13, 07:11 PM #4AMD Ryzen 7 7800X3D: Gigabyte X670 Aorus Elite AX: G.Skill Trident Z5 Neo RGB DDR5-6000 C30 : PowerColor Radeon RX 7900 GRE Hellhound OC: CORSAIR HX850i: Samsung 960 EVO 250GB NVMe: fiio e10k: lian-li pc-o11 dynamic XL:
-
2018-03-13, 07:13 PM #5
I'm going to go ahead and guess if your on team blue you like blue and if your on team red then you like red. What is good for your team counts. Whats bad for it is fake news.
-
2018-03-13, 07:15 PM #6
Ya it all kinda smells off their disclaimer is lol too https://amdflaws.com/disclaimer.html there plenty of other stuff about it too
"Legal Disclaimer BACK TO SITE CTS is a research organization. This website is intended for general information and educational purposes. This website does not offer the reader any recommendations or professional advice. **The opinions expressed in this report are not investment advice nor should they be construed as investment advice or any recommendation of any kind.
It summarizes security vulnerabilities, but purposefully does not provide a complete description of such vulnerabilities to protect users, such that a person with malicious intent could not actually exploit the vulnerabilities and try to cause harm to any user of the products described herein. Do not attempt to exploit or otherwise take advantage of the security vulnerabilities described in the website.
The report and all statements contained herein are opinions of CTS and are not statements of fact. To the best of our ability and belief, all information contained herein is accurate and reliable, and has been obtained from public sources we believe to be accurate and reliable. Our opinions are held in good faith, and we have based them upon publicly available facts and evidence collected and analyzed, which we set out in our research report to support our opinions. We conducted research and analysis based on public information in a manner that any person could have done if they had been interested in doing so. You can publicly access any piece of evidence cited in this report or that we relied on to write this report. Although we have a good faith belief in our analysis and believe it to be objective and unbiased, you are advised that we may have, either directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports. Any other organizations named in this website have not confirmed the accuracy or determined the adequacy of its contents.
You may republish this website in whole or in part as long as CTS is clearly and visibly credited and appropriately cited, and as long as you do not edit content.
Although we strive for accuracy and completeness to support our opinions, and we have a good-faith belief in everything we write, all such information is presented "as is," without warranty of any kind– whether express or implied – and CTS does not accept responsibility for errors or omissions. CTS reserves the right to change the contents of this website and the restrictions on its use, with or without notice, and CTS reserves the right to refrain from updating this website even as it becomes outdated or inaccurate"
-
2018-03-13, 07:17 PM #7
It's actually not a vulnerability...
All of the supposed attack vector relates to having Admin level privilege, which means the system has already been compromised. Which you know... is kind of pointless at that point anyways.
This is a stock manipulation scheme.
Their site even has this
https://amdflaws.com/disclaimer.html
They also have this clause in the white paperAlthough we have a good faith belief in our analysis and believe it to be objective and unbiased, you are advised that we may have, either directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports. Any other organizations named in this website have not confirmed the accuracy or determined the adequacy of its contents.
Basically saying they have the right to be wrong.Although we strive for accuracy and completeness to support our opinions, and we have a good faith belief in everything we write, all such information is presented "as is," without warranty of any kind whether express or implied and CTS does not accept responsibility for errors or omissions. CTS reserves the right to change the contents of this White Paper and the restrictions on its use, with or without notice, and CTS reserves the right to refrain from updating this White Paper even as it becomes outdated or inaccurate
-
2018-03-13, 07:28 PM #8
You failed to see my point, as far as their "Opinion whitepaper" goes ... it's a bit of meh.
The vulnerabilities they suggest again requires you to already have admin access, BIOS flash it with a modified BIOS that also installs Malware, install malware into the OS itself (which would require you to bypass UEFI BIOS checksum security with an encryption key only the companies have, barring ASUS' consumer line of boards) and only then do you have access.
No system is safe if it's this scenario as it would mean there's already a breach of access and compromised servers from within, barring the fact of previously mentioned malware in BIOS and OS.
BIOS infected malware already exists today and has existed for a long time, there's not a system safe in the world if you get into the BIOS.
I don't see this as a problem really because having physical access to a machine to allow that many operations unnoticed ... you're fucked regardless of platform."A quantum supercomputer calculating for a thousand years could not even approach the number of fucks I do not give."
- Kirito, Sword Art Online Abridged by Something Witty Entertainment
-
2018-03-13, 07:35 PM #9
-
2018-03-13, 07:44 PM #10AMD Ryzen 7 7800X3D: Gigabyte X670 Aorus Elite AX: G.Skill Trident Z5 Neo RGB DDR5-6000 C30 : PowerColor Radeon RX 7900 GRE Hellhound OC: CORSAIR HX850i: Samsung 960 EVO 250GB NVMe: fiio e10k: lian-li pc-o11 dynamic XL:
-
2018-03-13, 07:59 PM #11
No the point I'm trying to make is to make the vulnerabilities work you would already be compromised regardless.
Making the vulnerabilities almost completely useless.
As far as the Intel shit goes... honestly I don't disagree with what AMD fired back with considering that Intel's form of damage control was to involve AMD, it's main competitor, into the fray where they have had nothing to do with it.
If the competition is shit slinging your products as well for their own incompetence/malice then IMHO a vicious rebuttal is authorized."A quantum supercomputer calculating for a thousand years could not even approach the number of fucks I do not give."
- Kirito, Sword Art Online Abridged by Something Witty Entertainment
-
2018-03-13, 08:06 PM #12
-
2018-03-13, 08:15 PM #13
There are a few glaring problems with all of this:
1. All of the "flaws", with the exception of the ASRock flaw which is not actually an AMD flaw, require either physical access to flash the bios or elevated privileges.
2. The "company" announced to the press before they notified AMD.
3. There were a number of put options on AMD last week.
4. The "research paper" actually had the following in it. "In light of CTS’s discoveries, the meteoric rise of AMD’s stock price now appears to be totally unjustified and entirely unsustainable. We believe AMD is worth $0.00 and will have no choice but to file for Chapter 11 (Bankruptcy) in order to effectively deal with the repercussions of recent discoveries."
Some background on Viceroy: https://www.moneyweb.co.za/in-depth/...eroy-unmasked/
I can't see how Intel would be anywhere close to this. It's stock manipulation, pure and simple. I doubt the SEC would look too kindly on this sort of stuff.
-
2018-03-13, 08:15 PM #14
-
2018-03-13, 08:51 PM #15
-
2018-03-13, 08:55 PM #16
It's already being called into question. Look at the video and how they used stock backgrounds.
https://www.hardocp.com/news/2018/03...md_exploits_bs

-
2018-03-13, 09:19 PM #17Deleted
You realise Intel did have direct in their slides that AMD 'GLUED' together their cpus right?
And you realise things can only be proven if more then 1 company can produce the same results, why would any one believe a single company that already has a lot against it right now that came out of no where 'proving' this.
-
2018-03-13, 09:25 PM #18Scarab Lord


- Join Date
- Dec 2008
- Location
- One path
- Posts
- 4,907
I can only sum this up as a propaganda hit-job from FUD Intel or their fanboys. Your machine needs to already be compromised for a hacker to run any of these exploits.
If you knew the candle was fire then the meal was cooked a long time ago.
-
2018-03-13, 09:39 PM #19
AMD finally beating Intel.
1) Load the amount of weight I would deadlift onto the bench
2) Unrack
3) Crank out 15 reps
4) Be ashamed of constantly skipping leg day
-
2018-03-13, 09:50 PM #20
I doubt Intel has anything to do with this, there'd be too big of a backlash to this.
This is either some prank or someone trying to manipulate stocks as previously mentioned."A quantum supercomputer calculating for a thousand years could not even approach the number of fucks I do not give."
- Kirito, Sword Art Online Abridged by Something Witty Entertainment

 Recent Blue Posts
Recent Blue Posts
 Recent Forum Posts
Recent Forum Posts
 Do you consider the Horde to be "the bad guys" or is it more complex?
Do you consider the Horde to be "the bad guys" or is it more complex? MMO-Champion
MMO-Champion


 Reply With Quote
Reply With Quote





